OS Analysis
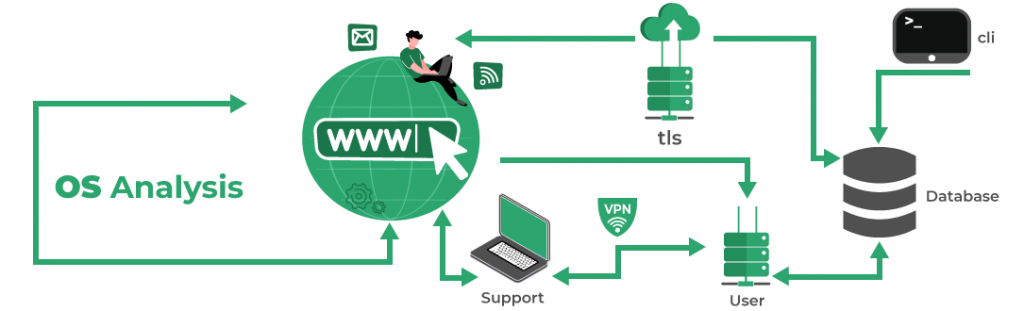
OS Analysis helps in crafting your operating systems’ queries using SQL statements. This feature makes it easier for the security engineers that are well aware of the SQL language. OS Analysis has multiple uses, uses that always prove to be beneficial for computer systems. While considering cybersecurity, this feature also comes in handy. SOCVault makes sure to be cautious yet vigilant at all times. Thus, the OS Analysis feature allows enhancing the endpoint security points.